 What Is Vishing Voice Phishing Scams Explained How To
What Is Vishing Voice Phishing Scams Explained How To
 Detecting And Characterizing Lateral Phishing At Scale The
Detecting And Characterizing Lateral Phishing At Scale The
 83 Of Global Respondents Experienced Phishing Attacks In
83 Of Global Respondents Experienced Phishing Attacks In
 Microsoft Remains The Most Usurped Brand As Phishing
Microsoft Remains The Most Usurped Brand As Phishing
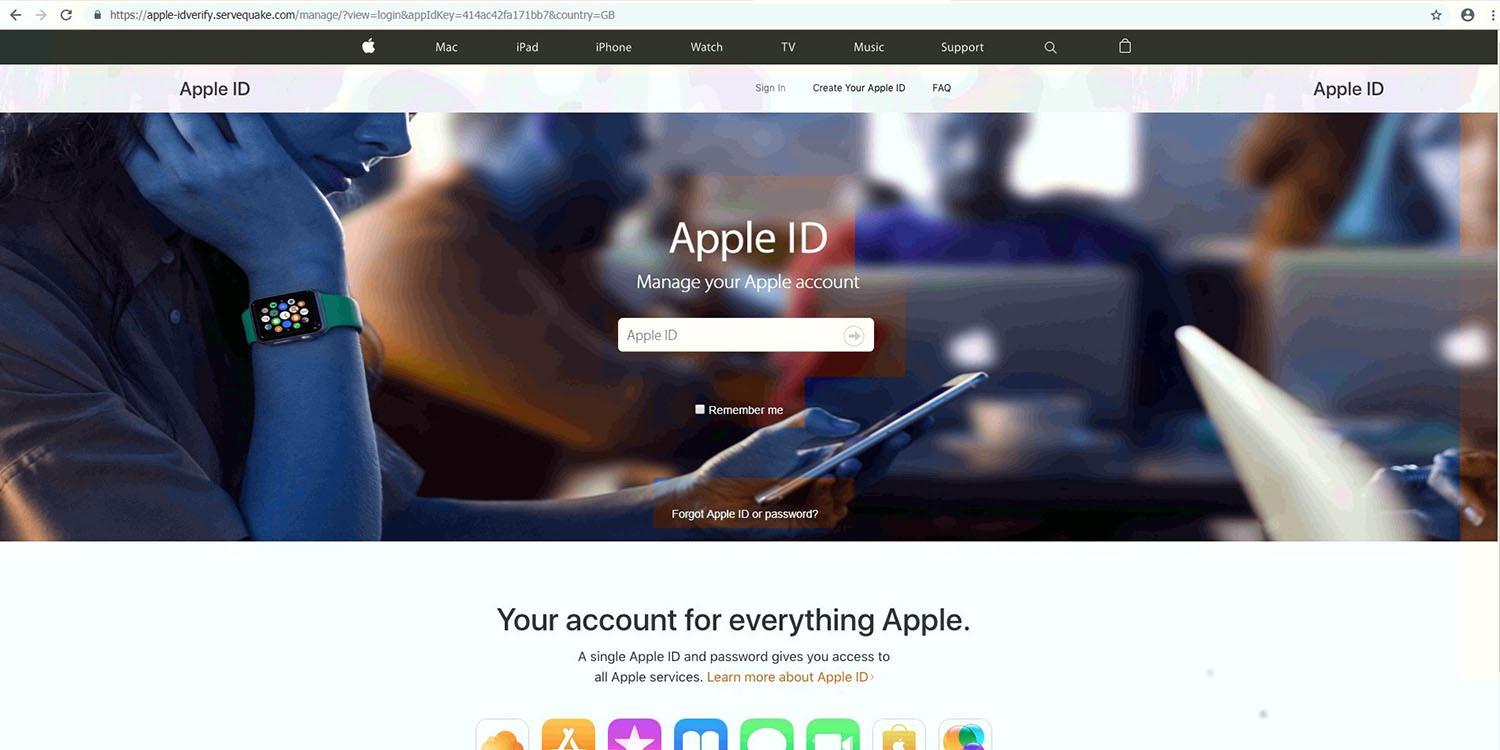 Phishing Attacks On Mac Users Doubling Heres What To Watch
Phishing Attacks On Mac Users Doubling Heres What To Watch
 The Dangers Of Phishing Scams And How To Protect Yourself
The Dangers Of Phishing Scams And How To Protect Yourself
 Phishing Attacks Breach Data Of 42k Florida Patients For 3
Phishing Attacks Breach Data Of 42k Florida Patients For 3
 The Ultimate Guide To Phishing
The Ultimate Guide To Phishing
 How To Prevent Phishing Attacks Emsisoft Security Blog
How To Prevent Phishing Attacks Emsisoft Security Blog
 Phishing Attacks 4 Ways You Can Defend Against Them
Phishing Attacks 4 Ways You Can Defend Against Them
 Social Engineering Security Wikipedia
Social Engineering Security Wikipedia
 What Is Phishing Attack Techniques Scam Examples Imperva
What Is Phishing Attack Techniques Scam Examples Imperva
 Ironscales Raises 15 Million To Defeat Phishing Attacks
Ironscales Raises 15 Million To Defeat Phishing Attacks
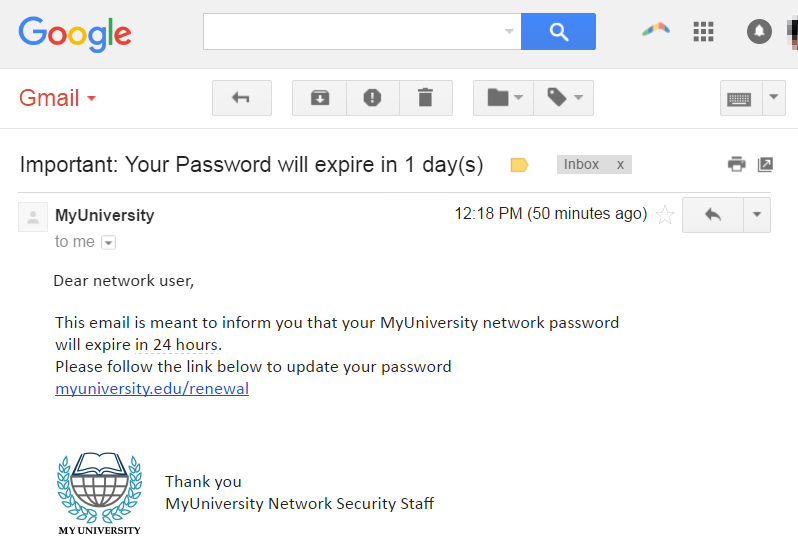
 5 Common Phishing Techniques Vade Secure
5 Common Phishing Techniques Vade Secure
 Social Engineering Explained How Criminals Exploit Human
Social Engineering Explained How Criminals Exploit Human
 Analyzing Spear Phishing Attacks
Analyzing Spear Phishing Attacks